Singapore
Surveillance


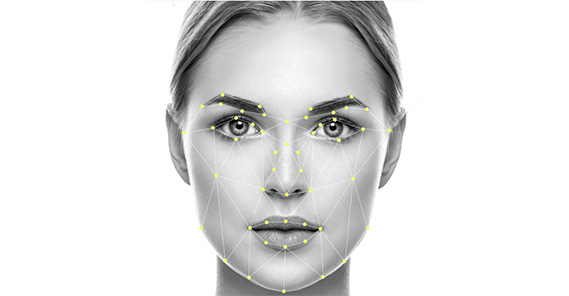
In today’s IoT era, security concerns have become a priority. As a result, there has been an increase in the use of camera surveillance. Its effectiveness, however, is limited to the availability of human resource to monitor the data. A better method of analysis is needed -- tireless AI-based technologies which can scan video footage to identify unusual behavior and then generate automated alerts.
Mega Events Surveillance
In today's connected, experience-focused world, entertainment expectations are high, and visitors want to enjoy sports events, concerts or theme parks unhindered by queues, crowds and archaic systems. At the same time, threats and anti-social behavior at large venues have persuaded mega-event goers that enjoyment must be underpinned by highly attentive and robust security. So how do competitive venue operators create a seamless but safe venue experience that satisfies their safety, cost and holistic service objectives?
Speed, accuracy and astute visitor analysis are of the essence. NEC's technologies and solutions satisfy all these requirements; offering the cutting-edge technology and the sophisticated AI, video and data analytics to astutely manage, direct and protect individuals.
Critical Infrastructure Surveillance
Airports, mass transit systems, power plants, telecommunication exchanges, water supply facilities. These pieces of critical infrastructure are all vital to the running of today's smart cities. And they all require round-the-clock, intelligent real-time monitoring to ensure efficient operation, minimize disruption from equipment investigations or outages, and shield against malicious physical intrusion or cyberattack.
NEC's integrated suite of advanced video analytics and multi-modal biometrics is designed to provide robust identification and access management for critical infrastructure across broad solution areas: real-time surveillance using the world's fastest and most accurate face recognition technology* and AI-driven video analytics; and behavior analysis for early detection of suspicious activity, abandoned objects or people requiring assistance.